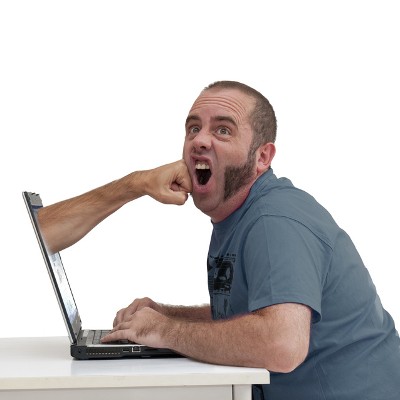
Too frequently, we hear stories about cyberattacks, software vulnerabilities turned tragic, and other pretty terrible situations for businesses. In an effort to help fight this, we’ve put together a list of handy tips for you so that you can be prepared to ward off threats.
ZR Systems Blog
We’ve all caught the obvious spam email, like the message that is clearly bogus, or the offer that is definitely too good to be true.
We’re going to confidently assume none of our readers are getting tricked by Nigerian Princes or getting roped into order virility drugs from an unsolicited email. The real threat comes from the more clever phishing attacks. Let’s take a look.
In a perfect world, keeping your antivirus updated and having a good firewall in place would be enough to protect your business from cybersecurity threats.
Bar none, cybersecurity has to be a major consideration for every business owner or manager in business today. The prevalence of people looking to rip your company off has never been higher; and that is the truth for nearly every company that uses the Internet for anything. Today, we take a look at some of the most serious cybersecurity threats that everyone should be cognizant of right now.
Two-factor authentication, also known as 2FA, is a very beneficial addition to consider for your cybersecurity. However, a research study unearthed a few surprising takeaways that indicate that 2FA may not be adopted as much as one might expect it to be.
Today’s headlines are peppered with stories of major companies and institutions falling victim to a cyberattack. As a business owner, what’s your response to these gut-wrenching stories? If you write them off as fear mongering and believe that these attacks can never happen to your SMB, well, you’re wrong. They can and it’s up to you to prevent such a disaster.
Data breaches are common problems for businesses of all shapes and sizes. In fact, they often have huge repercussions that aren’t initially seen in the heat of the moment. How can you make sure that a data breach won’t negatively impact your business, even well after you’ve fixed the initial problem?
If you panic in the event of a hacking attack, imagine how the National Security Agency (NSA) feels knowing that some of its exploits are for sale on the black market. While there isn’t any proof that the NSA has been breached, there’s evidence to suspect that their exploits are available for purchase on the black market. This means that a willing hacker could get their hands on government-grade hacking tools--a dangerous concept.
Businesses need to take security into account and make it a priority. In fact, security is so important that Verizon has compiled a report of the various types of attacks and data breaches that occurred in the past year. This is Verizon’s Data Breach Investigations Report, or DBIR, and it offers insights into how you can protect your business and secure your assets.
A vulnerability has been discovered that affects all versions of Microsoft’s Windows operating system, including the long-unsupported Windows XP, going all the way back to Windows 95. The vulnerability, called BadTunnel, allows attackers to directly bypass system defenses and initiate a man-in-the-middle attack. The vulnerability isn’t limited to just Windows, either; it also affects Internet Explorer, Edge, and other Microsoft software.
When it comes to cybersecurity, maintenance is key. Whether you choose human-based security or an automated security solution, running into shortcomings is still possible. Human security tends to rely on the word of experts, and anything that doesn’t fit into the guidelines is missed and may therefore get through and wreak havoc. Network security can be a touch overzealous, in a way “crying wolf,” with an excess of false positives that ultimately require human analysis, leading to human frustration.
Mobile? Grab this Article